firewalld 0.4.2 release
The new firewalld version 0.4.2 is available with enhancements, bug fixes and very nice speed ups.
The main changes are
New transaction model
Changes are done in one big transaction instead of smaller ones. This speeds up firewalld start and restart tremendously. The start is done up to in six or nine calls to the restore commands depending on the configuration. This depends on ipset and also direct configuration usage. Also all other actions benefit from this change.
Enhanced handling of connections and interfaces
For interfaces that are handled by NetworkManager, requests to add or change bindings are directed to NetworkManager in the firewall-cmd and firewall-config tools. For interfaces on Fedora and RHEL systems that are not handled by NM, there is a new mechanism that changes the ifcfg file if there is one using the interface. This makes zone interface bindings more consistent.
Usability enhancements for firewall-config
firewall-config has a new side bar with the active bindings of connections, interfaces and also sources. With this side bar it is possible to change the binding assignments in a simple way. A new overlay message window if the connection to firewalld could not be established or if it is lost. Speed ups for view changes runtime to permanent and back by introduction of new D-Bus methods in firewalld. The resize behavior has been fixed to be more expected.
Enhanced runtime to permanent migration
The enhanced migration is not saving interfaces that are under control of NetworkManager to the permanent configuration. Zones, services etc. are only migrated if there are changes compared to current permanent configuration.
New ICMP block inversion
The ICMP block is now completely handled per zone. With the new ICMP block inversion flag in the zone it is possible to invert the ICMP block. That means that the enabeld ICMP blocks are allowed and all others are blocked. In a drop zone these remaining types are dropped and not blocked. The logging of denied rules have been added to icmp-blocks.
Source port support in zones, services and rich rules
Additionally to ports is it also now possible to allow source ports in a zones and also in a service in a similar way as existing ports. There is a new flag source-port for this. Source ports can also be used in rich rules as elements. The source ports can be combined with logging, limiting and also an action.
Rich rules with destination only
Destination addresses can now be used in rich rules without an element. This enabled the use of rich rules containing destination addresses combined with an action and logging only.
There are also several other bug fixes or enhancements and code optimizations.
The new firewalld version 0.4.2 is available here:
- Tarball: firewalld-0.4.2.tar.gz
- SHA256: e127bff64f6e7c242668a971674f5f075657fc5110a6ab363129be243885f938
- Source repository on github: v0.4.2
- Complete changelog on github: 0.4.1.2 to 0.4.2
More firewalld speed ups
Previously firewalld got a nice speed up by using the iptables restore commands, that made it possible to commit several changes at once. Now there is also a transaction model using these commands, which enables firewalld to apply lots of rules at once. For example to apply a single zone or also to apply the default rules and all zones while loading.
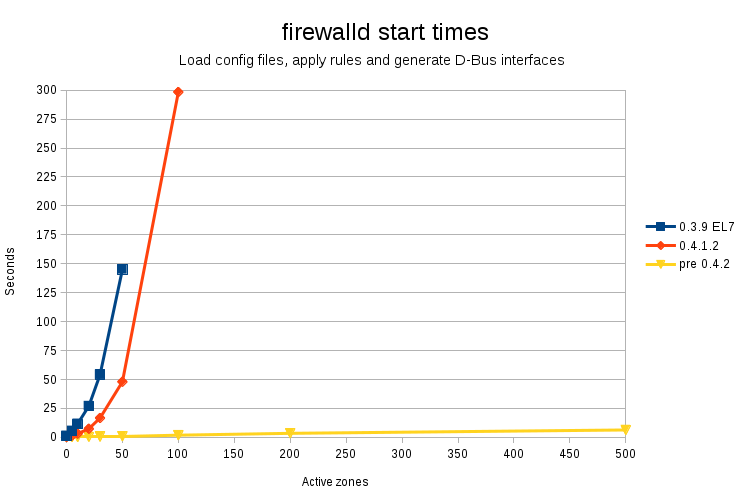
Here are some comparison numbers of the old firewalld version 0.3.9 in RHEl-7.2, the actual firewalld version 0.4.1.2 and the development version 0.4.2 that will be released soon.
The diagram shows the time that is needed to start firewalld with loading of all config files, applying all rules and the generation of the D-Bus interfaces.
Each of the zones has 5 interface bindings which are therefore active and also applied.
Here is the table with all numbers:
| Active zones | 0.3.9 EL7 | 0.4.1.2 | pre 0.4.2 |
|---|---|---|---|
| 0 | 317 - 1.32s | 335 - 0.31s | 335 - 0.18s |
| 5 | 1037 - 5.59s | 1055 - 1.53s | 1055 - 0.19s |
| 10 | 1757 - 11.69s | 1775 - 3.11s | 1775 - 0.24s |
| 20 | 3197 - 27.00s | 3215 - 7.35s | 3215 - 0.40s |
| 30 | 4637 - 54.08s | 4655 - 16.65s | 4655 - 0.49s |
| 50 | 7517 - 145.01s | 7535 - 47.95s | 7535 - 0.90s |
| 100 | 14735 - 298.34s | 14735 - 1.81s | |
| 200 | 29135 - 3.40s | ||
| 500 | 72335 - 6.33s | ||
| 1000 | 144335 - 13.35s |
The empty fields are not bench marked anymore, because it will take too much time. The first number in the cells is the number of rules. Since firewalld version 0.4.1.2, there are some extra rules because of a better way to handle zones with accept, reject or drop targets.
The number of rules is gathered with the command
(iptables-save; ip6tables-save; ebtables-save) | wc -l
The firewalld start method has been extended with time callsin the beginning and the end to get the time difference.
The test are done on a Lenovo ThinkPad T510 with an i7M620 CPU and a normal HDD running RHEL-7.2. The ebtables package has been patched with the upstream noflush patch for ebtables-restore. Without this option firewalld will not use ebtables-restore. The tested firewalld version 0.4.1.2 additionally contains a fix for ebtables-restore usage.
firewalld 0.4.1.2 release
The new firewalld version 0.4.1.2 is available with enhancements, bug fixes and speed ups.
The main changes are
ipset handling enhancements
No cleanup of ipsets using timeouts while reloading.
Only destroy ipsets with the same name and a conflicting type or conflicting options.
Use ipset types that are supported by the system.
Add and remove several ipset entries in one call using a file
The new options for firewall-cmd are –add-entries-from-file and –remove-entries-from-file.
Reduced time frame where builtin chains are on policy DROP while reloading
All config files are read before the rule set will be created. This is good on slower machines and also reduced the possibility of packet losses while reloading.
Command line interface support to get and alter descriptions
The new options for firewall-cmd and firewall-offline-cmd are –set-description, –get-description, –set-short and –get-short for zones, services, ipsets and icmptypes.
Fixed logging in rich rule forward rules
Rework of import structures
Reduced calls to get ids for port and protocol names
NetworkManager module
This module is used to get and set zones of connections, used in firewall-applet and firewall-config.
Autodetection of backend tools in configure
The {ip,ip6,eb}tables{,-restore} and ipset backend tools are discovered in the build process to use a proper path automatically. The with options for these tools in configure are still usable for overloading.
D-Bus properties in introspection data
The D-Bus properties are now part of the introspection data and are now visible in D-Bus viewers and debuggers.
There are also several bug fixes and further code optimizations.
The new firewalld version 0.4.1.2 is available here:
- Tarball: firewalld-0.4.1.2.tar.gz
- SHA256: fa818f2bf6a500cd81968db0ab8c6220a74b78c3a3fc4b2d7663daed003b6a34
- Source repository on github: v0.4.1.2
- Complete changelog on github: 0.4.1.1 to 0.4.1.2
firewalld 0.4.0 release
The new firewalld version 0.4.0 is available with amazing new features like ipset support, MAC address support, logging of denied packets, enhancements and speed ups.
The main changes are
Speed ups
The load, reload, restart and stop of firewalld ha sbeen sped up a lot by enabling the use of the restore commands of iptables, ip6tables and ebtables. Rules are now applied in bigger chunks, which speeds up all actions of firewalld that are changing firewall rules in netfilter.
The new setting IndividualCalls has been added to firewalld.conf. The setting defaults to no, which enabled the use of the restore commands.
The use of the restore commands might not fit all needs and is also resulting in less detailed error messages. Additionally the restore commands are not supporting the locking mechanisms. If the use of the restore commands is not possible for the use case, then the IndividualCalls settiung should be enabled.
The use of ebtables-restore is limited to future versions, that will support the –noflush option. This option has already been added to the upstream git repository, but is not part of a release, yet.
ipset support
ipsets can now be used as zone bindings and also in rich rules.
firewalld supports initially the use of hash:ip, hash:net and hash:mac types. The use of ipsets with timeout is also possible, but the entries in the ipset then need to be taken care directly with ipset.
For simple black and white listing the use of ipsets is recommended altogether with rich rules.
MAC address support
MAC addresses can now also be used directly for zone bindings and in rich rules. A use of MAC addresses in ipsets is also possible.
Log of denied packets
The new LogDenied setting has been added to firewalld.conf. It can be altered with the command line tools and also firewall-config.
If LogDenied is enabled, logging rules right before reject and drop rules in the INPUT, FORWARD and OUTPUT chains for the default rules and also final reject and drop rules in zones. Possible values for LogDenied are: all, unicast, broadcast, multicast and off.
Mark action in rich rules
With the mark action it is now possible to mark packets matching the rich rule parameters.
The mark action results in -j MARK –set-xmark <mark> in the PREROUTING chain in the mange table to be able to affect routing with iproute.
Enhanced alteration of config files with command line tools
The permanent zone, service, icmptype and ipset config files can now directly be edited with the command line tools firwall-cmd and firewall-offline-cmd.
Use of zone chains in direct interface
The use of zone specific log, deny and allow chains is now possible in direct rules and tracked passthrough rules.
The needed parts of the zone structure are created on reload if one of the zone chains is used in the direct interface. The remaining parts of the zone are created as soon as it is used with a binding of if it is the default zone.</p>
firewall-applet
The firewall-applet has been further extended after the Qt migration and now supports the same functionality as the Gtk version before and even a bit more.
It provides now a global settings file in /etc/firewall/applet.conf and also a user settings file in $HOME/.config/firewall/applet.conf
New services
The services ceph-mon, ceph, docker-registry, imap, pop3, pulseaudio, smtps, snmptrap, snmp, syslog-tls and syslog have been added.
There are also several bug fixes and further code optimizations.
The new firewalld version 0.4.0 is available here:
- Tarball: firewalld-0.4.0.tar.gz
- SHA256: 97f13b9fe28d7be7726ecc7d09a2ec85d47efade9859d0d0e37f426bc142f64b
- Source repository on github: v0.4.0
- Complete changelog on github: 0.3.14.2 to 0.4.0
firewalld speed up
Since end of last year firewalld supports to use the restore commands of iptables, ip6tables and ebtables.This means that rules do not need to get applied one by one, but in bigger chunks. This results for example in a nice speed up of the firewalld start, reload, restart and stop.
The default rules are applied using these commands in one. The changes for example for services, ports etc. are applied per service, port etc. to be able to give feedback per item. Enabling or disabling single ports are therefore not sped up by this, but services using several ports are.
The use of the restore commands is also the base to be able to add direct rule sets, that are applied in one step as a whole.
The new setting IndividualCalls has been introduced to disable the use of the restore commands and to use iptables, ip6tables and ebtables individual calls per rule.
There are two limitations with using the restore commands:
- The restore commands in the iptables package need to extended to use the locking mechanism in xtables and ebtables to prevent clashes with concurrent calls of ip*tables and ebtables. Enabling IndividualCalls in the firewalld configuration file is helping here, but disables the use of the restore commands.
- The error reporting is a not as verbose as with single commands. An enhancement here is possible, but not to the same extend as with single calls.